[ad_1]

Aurich Lawson | Getty Photographs
A large flood of malicious site visitors that not too long ago set a brand new distributed denial-of-service file got here from an unlikely supply. A botnet of simply 5,000 units was accountable, as extortionists and vandals proceed to develop ever extra highly effective assaults to knock websites offline, safety researchers stated.
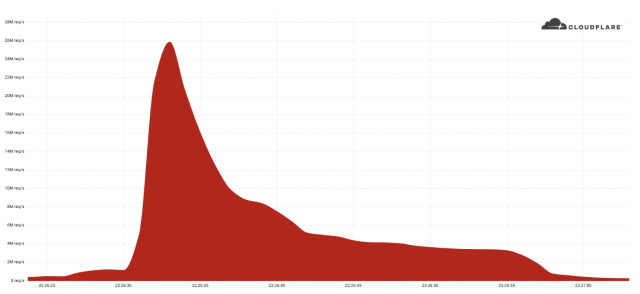
The DDoS delivered 26 million HTTPS requests per second, breaking the earlier file of 15.three million requests for that protocol set solely seven weeks ago, Cloudflare Product Supervisor Omer Yoachimik reported. In contrast to extra widespread DDoS payloads resembling HTTP, SYN, or SYN-ACK packets, malicious HTTPS requests require significantly extra computing sources for the attacker to ship and for the defender or sufferer to soak up.
4,000 instances stronger
“We have seen very massive assaults up to now over (unencrypted) HTTP, however this assault stands out due to the sources it required at its scale,” Yoachimik wrote.
Cloudflare
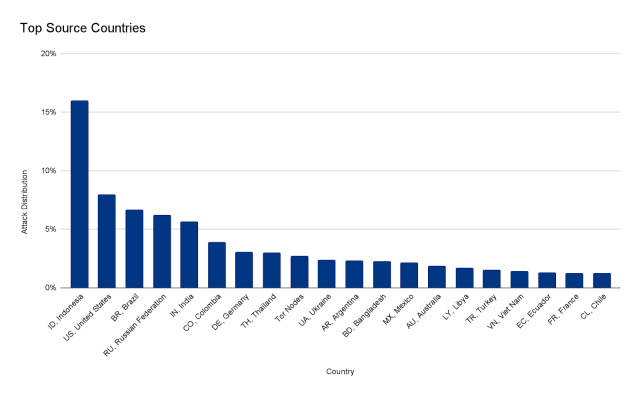
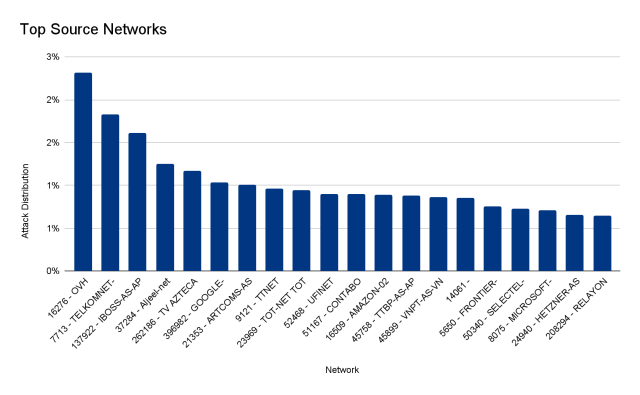
The burst lasted lower than 30 seconds and generated greater than 212 million HTTPS requests from greater than 1,500 networks in 121 nations, with Indonesia, the USA, Brazil, and Russia topping the checklist. The highest networks used included French-based OVH (Autonomous System Quantity 16276), the Indonesian Telkomnet (ASN 7713), the US-based iboss (ASN 137922), and the Libyan Ajeel (ASN 37284). About three % of the assault got here by way of Tor nodes.
Cloudflare
Cloudflare
As was the case with the earlier 15.three million-HTTPS-requests-per-second assault, the brand new one originated primarily on units from cloud service suppliers. The servers and digital machines out there from these suppliers are significantly extra highly effective than compromised computer systems and IoT units linked to residential ISPs, that are the extra widespread supply of DDoSes.
Yoachimik wrote:
The 26M rps DDoS assault originated from a small however highly effective botnet of 5,067 units. On common, every node generated roughly 5,200 rps at peak. To distinction the dimensions of this botnet, we’ve been monitoring one other a lot bigger however much less highly effective botnet of over 730,000 units. The latter, bigger botnet wasn’t capable of generate a couple of million requests per second, i.e. roughly 1.three requests per second on common per system. Placing it plainly, this botnet was, on common, 4,000 instances stronger on account of its use of digital machines and servers.
In some instances, DDoSers mix their use of cloud-based units with different strategies to make their assaults stronger. Within the 15.three million-HTTPS-requests-per-second DDoS from earlier this yr, for instance, Cloudflare uncovered proof that the risk actors might have exploited a critical vulnerability. This exploit allowed them to bypass authentication in a variety of Java-based purposes used contained in the cloud environments working their assault units.
DDoS assaults may be measured in a number of methods, together with by the amount of knowledge, the variety of packets, or the variety of requests despatched every second. The opposite present information are 3.4 terabits per second for volumetric DDoSes—which try to devour all bandwidth out there to the goal—and 809 million packets per second. The 26 million HTTPS requests per second break the earlier 17.2 million-requests-per-second file set in 2020. Not solely did that earlier assault ship fewer packets than the brand new file, but it surely additionally relied on HTTP, which is not as potent as HTTPS.
The Cloudflare product supervisor stated that his firm robotically detected and mitigated the assault in opposition to the client, which was utilizing Cloudflare’s free service.
Source link


