[ad_1]
For years, malicious hackers have been hacking massive fleets of MikroTik routers and conscripting them into Trickbot, one of many Web’s most harmful botnets. Now, Microsoft has lastly found out why and the way the routers are being put to make use of.
Trickbot came to light in 2016 as a trojan for stealing account passwords to be used in financial institution fraud. Since then, Trickbot has mushroomed into one of many Web’s most aggressive risk platforms, because of its extremely modular, multistage malware framework that gives a full suite of instruments which can be used to put in ransomware and different types of malware from different hacking teams.
The malware driving Trickbot is notable for its superior capabilities. It excels at gaining highly effective administrator privileges, spreading quickly from pc to pc in networks, and performing reconnaissance that identifies contaminated computer systems belonging to high-value targets. The malware typically makes use of available software program like Mimikatz or exploits like EternalBlue, which was stolen from the Nationwide Safety Company.
Hiding the C2
Trickbot operators, Microsoft said on Wednesday, are compromising MikroTik gadgets and utilizing these gadgets to hide the placement of the command and management servers that change knowledge and instructions with contaminated computer systems. As a substitute of contaminated computer systems connecting on to the management servers, the computer systems hook up with the compromised routers, which act as go-betweens.
When safety analysts monitor the connections contaminated computer systems make, the researchers see IP addresses belonging to compromised routers inside properties and companies. The situation of the management servers themselves stays hidden and might’t be detected with out entry to the proxy router. Right here’s an outline:
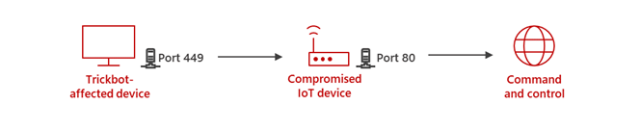
Microsoft
“The aim of Trickbot utilizing MikroTik gadgets is to create a line of communication between the Trickbot-affected gadget and the C2 server that customary protection techniques within the community are usually not in a position to detect,” Microsoft researchers wrote. “The attackers start by hacking right into a MikroTik router.”
Microsoft stated a chief purpose Trickbot has such an affinity for MikroTik is MikroTik’s distinctive Linux-based RouterOS. This working system permits customers to remotely pipe instructions that use the SSH, or safe shell, protocol. The flexibleness and energy of the instructions make MikroTik routers a super proxy. Trickbot operators can ship a single command that causes massive numbers of the gadgets to funnel visitors in particular methods which can be helpful to the botnet structure.
The instructions, that are preceded by “/”, embrace issues like /ip, /system, and /software. They gained’t usually work on common Linux-based shell home windows. MikroTik shells, against this, provide Trickbot operators a menu of helpful choices. For instance, one command Microsoft noticed Trickbot sending was:
/ip firewall nat add chain=dstnat proto=tcp dst-port=449 to-port=80 motion=dst-nat to-addresses= dst-address=
That command creates a brand new rule, much like iptables, that receives knowledge from compromised computer systems by means of port 449. The command then redirects knowledge by means of port 80 to command TrickBot servers.
“The stated command is a reputable community tackle translation (NAT) command that enables the NAT router to carry out IP tackle rewriting,” Microsoft researchers defined. “On this case, it’s getting used for malicious exercise. Trickbot is understood for utilizing ports 443 and 449, and we had been in a position to confirm that some goal servers had been recognized as TrickBot C2 servers up to now.”
get owned, tips on how to keep clear
Trickbot makes use of a number of strategies to compromise the routers. These strategies embrace:
- Exploiting gadgets that also use default MikroTik passwords
- Performing password-guessing assaults, probably utilizing passcodes harvested from different MikroTik gadgets
- Exploiting CVE-2018-14847 on gadgets with RouterOS variations older than 6.42. This crucial vulnerability provides the attacker the power to learn arbitrary information like person.dat, which comprises passwords. Analysis from final 12 months discovered that CVE-2018-14847 was one in all three critical vulnerabilities present in 300,000 MikroTik routers.
As soon as the operators take management of a tool, they alter the password to stop anybody else from remotely regaining management.
Source link


