[ad_1]

Getty Pictures
Whenever you use your telephone to unlock a Tesla, the system and the automotive use Bluetooth alerts to measure their proximity to one another. Transfer near the automotive with the telephone in hand, and the door mechanically unlocks. Transfer away, and it locks. This proximity authentication works on the belief that the important thing saved on the telephone can solely be transmitted when the locked system is inside Bluetooth vary.
Now, a researcher has devised a hack that permits him to unlock thousands and thousands of Teslas—and numerous different gadgets—even when the authenticating telephone or key fob is a whole lot of yards or miles away. The hack, which exploits weaknesses within the Bluetooth Low Vitality commonplace adhered to by 1000’s of system makers, can be utilized to unlock doorways, open and function automobiles, and acquire unauthorized entry to a bunch of laptops and different security-sensitive gadgets.
When comfort comes again to chew us
“Hacking right into a automotive from a whole lot of miles away tangibly demonstrates how our linked world opens us as much as threats from the opposite facet of the nation—and generally even the opposite facet of the world,” Sultan Qasim Khan, a principal safety advisor and researcher at safety agency NCC Group, instructed Ars. “This analysis circumvents typical countermeasures towards distant adversarial automobile unlocking and modifications the best way we’d like to consider the safety of Bluetooth Low Vitality communications.”
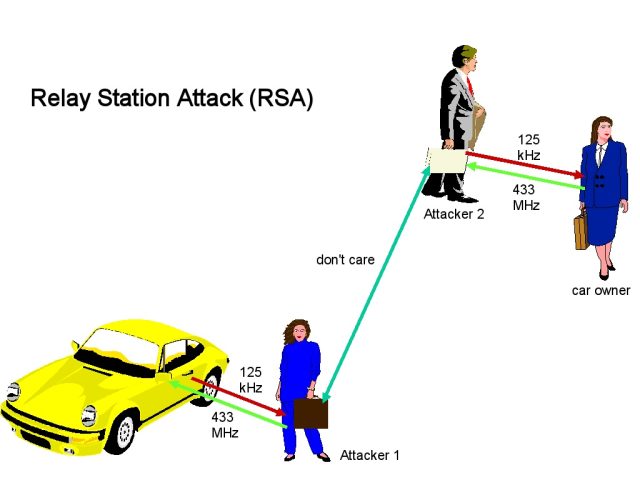
This class of hack is called a relay attack, a detailed cousin of the person-in-the-middle attack. In its easiest kind, a relay assault requires two attackers. Within the case of the locked Tesla, the primary attacker, which we’ll name Attacker 1, is in shut proximity to the automotive whereas it’s out of vary of the authenticating telephone. Attacker 2, in the meantime, is in shut proximity to the respectable telephone used to unlock the automobile. Attacker 1 and Attacker 2 have an open Web connection that permits them to trade information.
Attacker 1 makes use of her personal Bluetooth-enabled system to impersonate the authenticating telephone and sends the Tesla a sign, prompting the Tesla to answer with an authentication request. Attacker 1 captures the request and sends it to Attacker 2, who in flip forwards the request to the authenticating telephone. The telephone responds with a credential, which Attacker 2 promptly captures and relays again to Attacker 1. Attacker 1 then sends the credential to the automotive.
With that, Attacker 1 has now unlocked the automobile. Right here’s a simplified assault diagram, taken from the above-linked Wikipedia article, adopted by a video demonstration of Khan unlocking a Tesla and driving away with it, though the approved telephone isn’t wherever close by.
Wikipedia
NCC Group demo Bluetooth Low Vitality hyperlink layer relay assault on Tesla Mannequin Y.
Relay assaults in the true world needn’t have two precise attackers. The relaying system could be stashed in a backyard, coat room, or different out-of-the-way place at a house, restaurant, or workplace. When the goal arrives on the vacation spot and strikes into Bluetooth vary of the stashed system, it retrieves the key credential and relays it to the system stationed close to the automotive (operated by Attacker 1).
The susceptibility of BLE, quick for Bluetooth Low Vitality, to relay assaults is well-known, so system makers have lengthy relied on countermeasures to forestall the above state of affairs from occurring. One protection is to measure the movement of the requests and responses and reject authentications when the latency reaches a sure threshold, since relayed communications usually take longer to finish than respectable ones. One other safety is encrypting the credential despatched by the telephone.
Khan’s BLE relay assault defeats these mitigations, making such hacks viable towards a big base of gadgets and merchandise beforehand assumed to be hardened towards such assaults.
Source link


